Bachelor Project: Game-based learning in cyber security
Cyber Security · Game-Based Learning · Java · Bachelor Project
May 2024
The Problem
Here's a stat that stuck with me: 68% of data breaches involve a non-malicious human element. Not sophisticated zero-day exploits or nation-state hackers breaking through firewalls just regular people clicking the wrong link, reusing passwords, or leaving their screen unlocked.
Companies can invest millions in technical defenses, but if employees don't understand the basics of cyber security, all those firewalls are only as strong as the person sitting behind the keyboard. The challenge is that cyber security training is, for most people, painfully boring. Posters in the break room and mandatory e-learning modules aren't exactly inspiring anyone to change their habits.
That's the gap we wanted to close with our bachelor project: How can we convey cyber security information through a game-based learning platform?
The Idea
We built a desktop application that teaches fundamental cyber security concepts through an integrated snake game. Instead of passively reading about phishing or ransomware, users play a familiar, engaging game and answer cyber security questions as part of the gameplay.
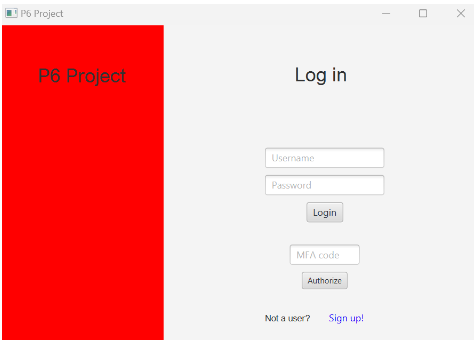
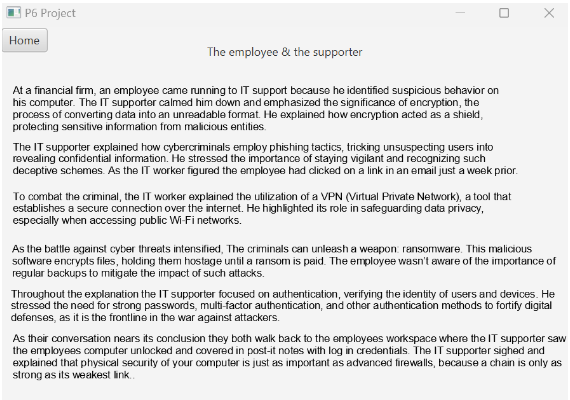
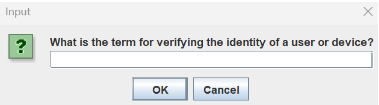
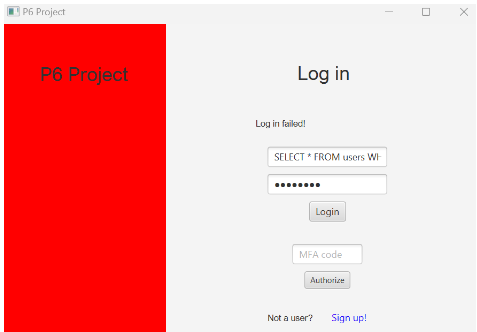
The platform works like this. Users sign up and log in with multi-factor authentication built in. They read a short fictional story about an employee learning cyber security from an IT supporter this story covers the key concepts needed to answer the in-game questions. Then they play a classic snake game. Every time the snake eats a piece of food, the game pauses and presents a cyber security question. Answer correctly and you keep playing. Answer wrong and the run ends. Scores and completion rates are saved to a leaderboard, fostering competition among users.
The competitive element was intentional. Research consistently shows that leaderboards are one of the most effective gamification tools for driving engagement, especially in the short term. We wanted colleagues to challenge each other, turning what would normally be a chore into something people actually want to do.
What We Built
The application was developed in Java using JavaFX for the GUI. On the backend, we used a MySQL database to store user accounts, game scores, and completion data. The architecture is straightforward a desktop client communicating with a local database but we put significant effort into the security side of things.
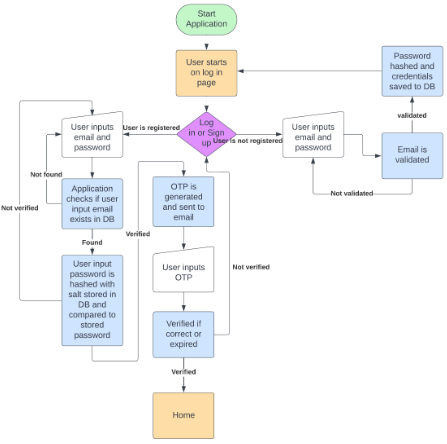
For authentication, we implemented a full multi-factor login flow. Users log in with an email and password, and then receive a one-time password sent to their email. The OTP has a five-minute expiration window and a three-attempt limit before resetting, which gives a brute-force attacker roughly a 0.0003% chance of guessing correctly.
Passwords are never stored in plaintext. We hash them using SHA-256 with a unique 16-byte salt per user, so even if the database were compromised, the passwords remain protected. All user inputs go through whitelist validation using Java regular expressions, and every database query uses prepared statements to guard against SQL injection attacks.
We also included an admin panel where administrators can view all game runs with their unique identifiers and delete entries from the scoreboard as needed.
The Research Behind It
Before building anything, we spent considerable time reviewing the literature on gamification and game-based learning. We looked at examples ranging from Kahoot in education to Aalborg University's own Haaukins platform for penetration testing training, PwC's "Game of Threats" cybersecurity simulation, and Google's Interland for teaching kids about online safety.
One distinction that shaped our approach was the difference between gamification and game-based learning. Gamification adds game elements like points and leaderboards to an existing process. Game-based learning goes further it embeds the learning directly into a game experience. We chose the latter, building an actual game that serves as the learning vehicle rather than just sprinkling badges onto a quiz.
We also reviewed different methods companies use to deliver security awareness: conventional posters and newsletters, instructor-led sessions, video-based content, simulation-based phishing tests, and game-based approaches. Each has trade-offs, but game-based methods stood out for their ability to actively engage users rather than relying on passive consumption.
Testing and Results
We conducted a user test with five participants, following the principle from usability research that testing beyond five users yields rapidly diminishing returns since most will encounter the same issues.
The results were encouraging. All participants found the game fun and were positively surprised by learning through gameplay. Navigation was intuitive, and most users figured out the sign-up and login flow quickly, even with the multi-factor step. When users failed their first game attempts without reading the story, they went back and read it before trying again exactly the learning behavior we were hoping for.
The constructive feedback was also valuable and expected. The GUI needed significant visual polish. The question pool felt repetitive after a few rounds. The story, while functional, read like it had been written around the questions rather than as a naturally engaging narrative. These are all things we'd prioritize in future iterations.
On the security side, we tested the application against common SQL injection attacks and confirmed that the whitelist validation and prepared statements blocked them effectively.
What I Learned
This project reinforced something I believe strongly: how you deliver information matters as much as the information itself. Cyber security fundamentals aren't complicated, but getting people to care enough to learn them is the real challenge. Game-based learning isn't a silver bullet, but our results along with the broader research show it has real potential to make security training something people engage with willingly.
On the technical side, building the full stack from authentication to database to game engine gave me hands-on experience with security best practices that I'd only read about before. Implementing hashing with salts, designing input validation, and thinking through attack vectors from a dark user story perspective made the security concepts concrete in a way that textbook study alone never could.
If I were to continue this project, the first priorities would be expanding the question pool significantly, replacing the story with a video-based narrative for better engagement, implementing a proper modern GUI, and moving the database to the cloud so the platform could be used across an organization.
The Bottom Line
Our application is a small proof of concept, but it demonstrates something important: when you make learning interactive and competitive, people pay attention. In a world where the majority of breaches come down to human error, finding better ways to educate people about cyber security isn't just an academic exercise it's a practical necessity.
